
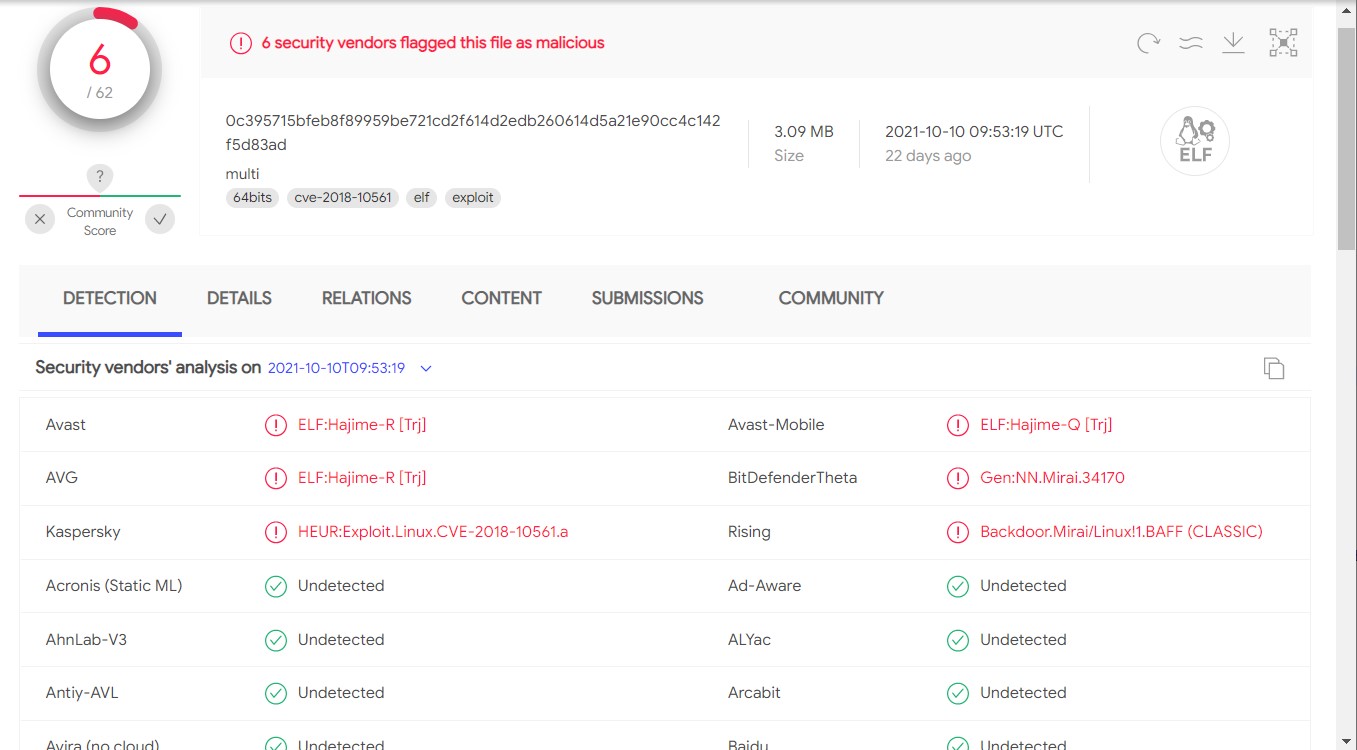
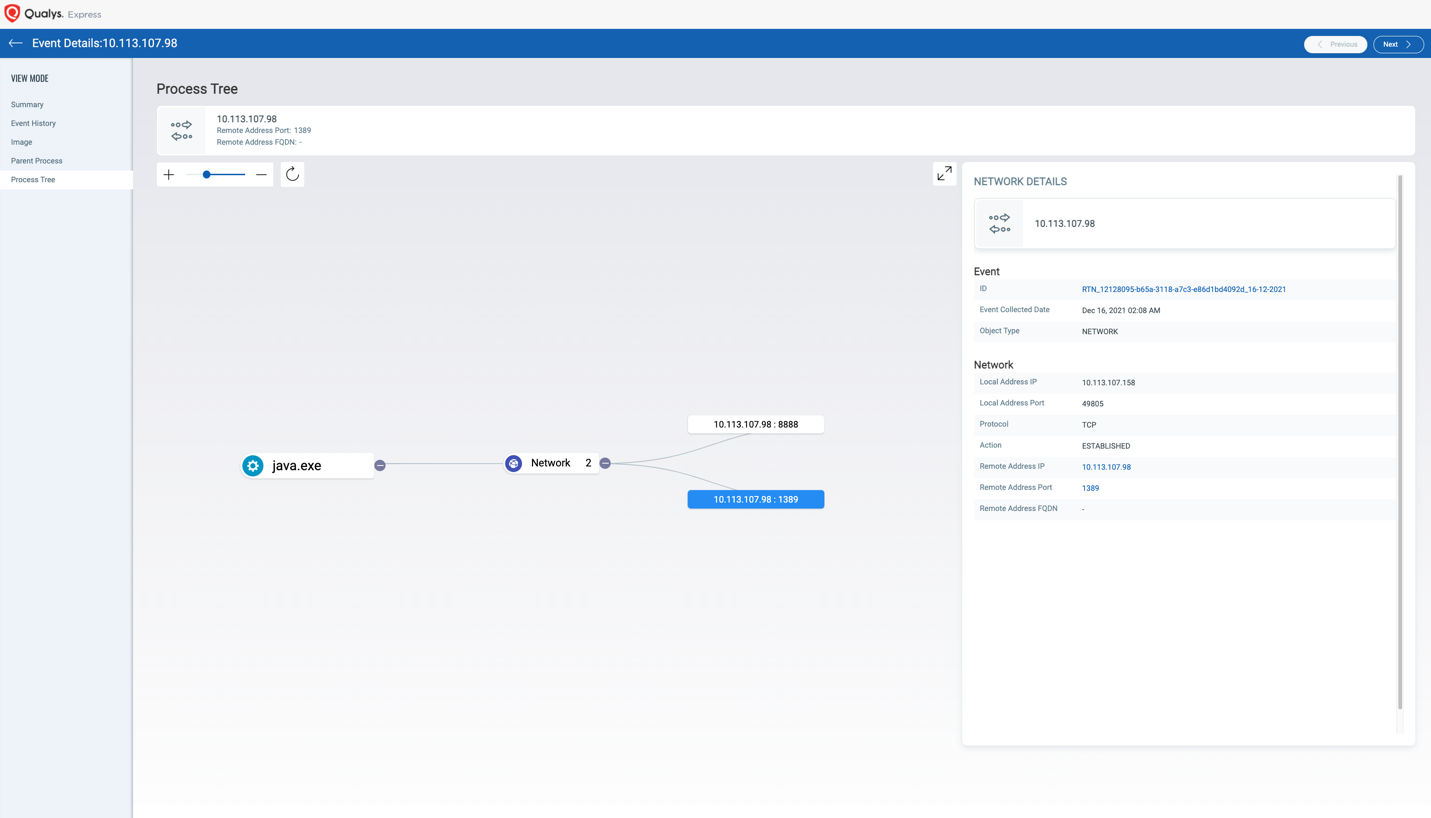
Guidance for preventing, detecting, and hunting for exploitation of the Log4j 2 vulnerability - Microsoft Security Blog
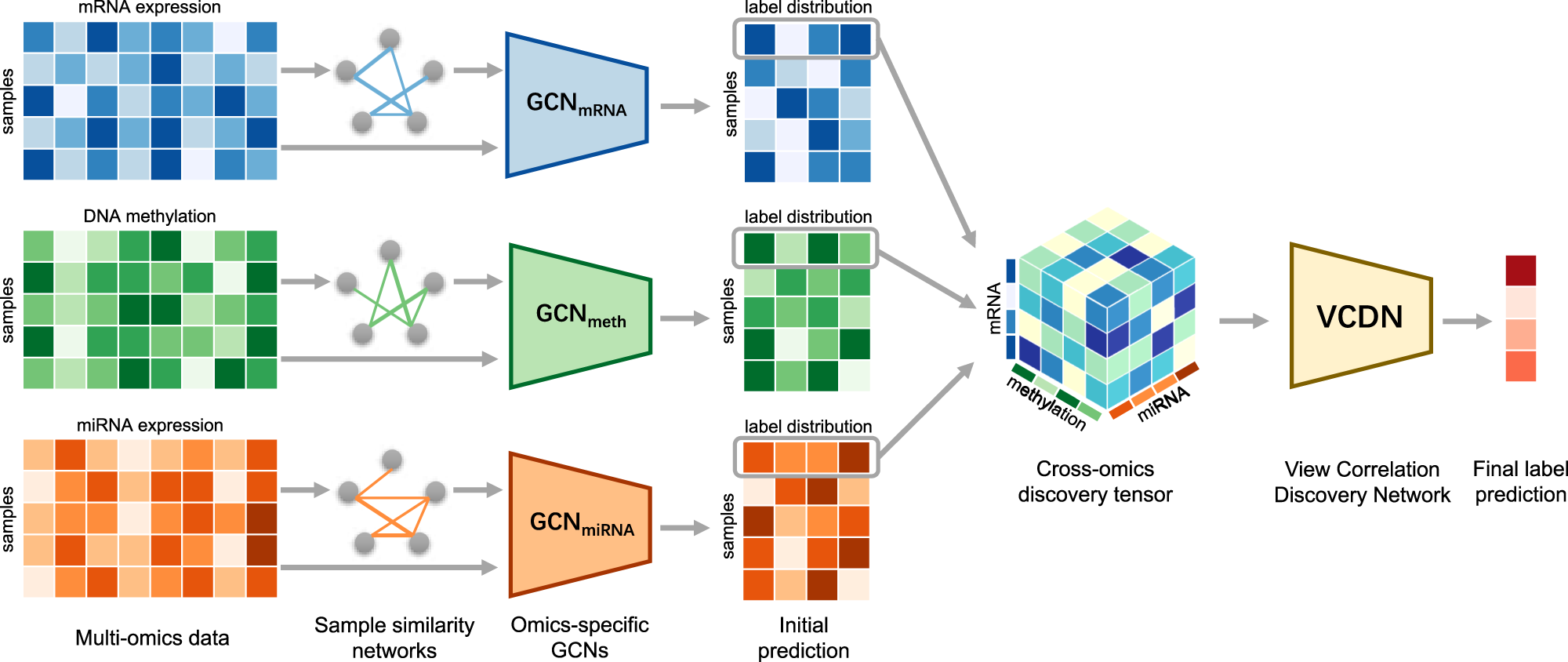
MOGONET integrates multi-omics data using graph convolutional networks allowing patient classification and biomarker identification | Nature Communications
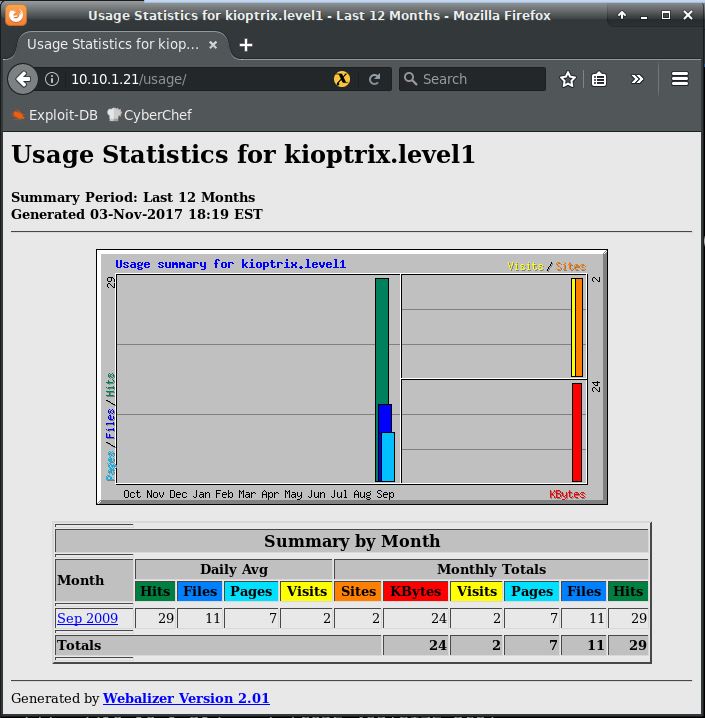










![PDF] MRTG: The Multi Router Traffic Grapher | Semantic Scholar PDF] MRTG: The Multi Router Traffic Grapher | Semantic Scholar](https://d3i71xaburhd42.cloudfront.net/47193673835e0e8bd9480558e40ac5eb5993045f/7-Figure7-1.png)



